Why Identity Execution Needs Governance — Not Just Authentication

Introduction
For decades, enterprise identity systems have focused on one primary question:
“Is this user who they claim to be?”
Authentication systems answered that question well. Passwords evolved into MFA. Identity providers became centralized. Security improved.
But a critical gap remained — one that modern enterprises can no longer ignore:
Authentication answers who you are.
It does not allow you to control what you execute.
In today’s distributed, API-driven, multi-system environments, identity is no longer just about access. It is about execution control under governance.
The Limitation of Authentication-Centric Identity
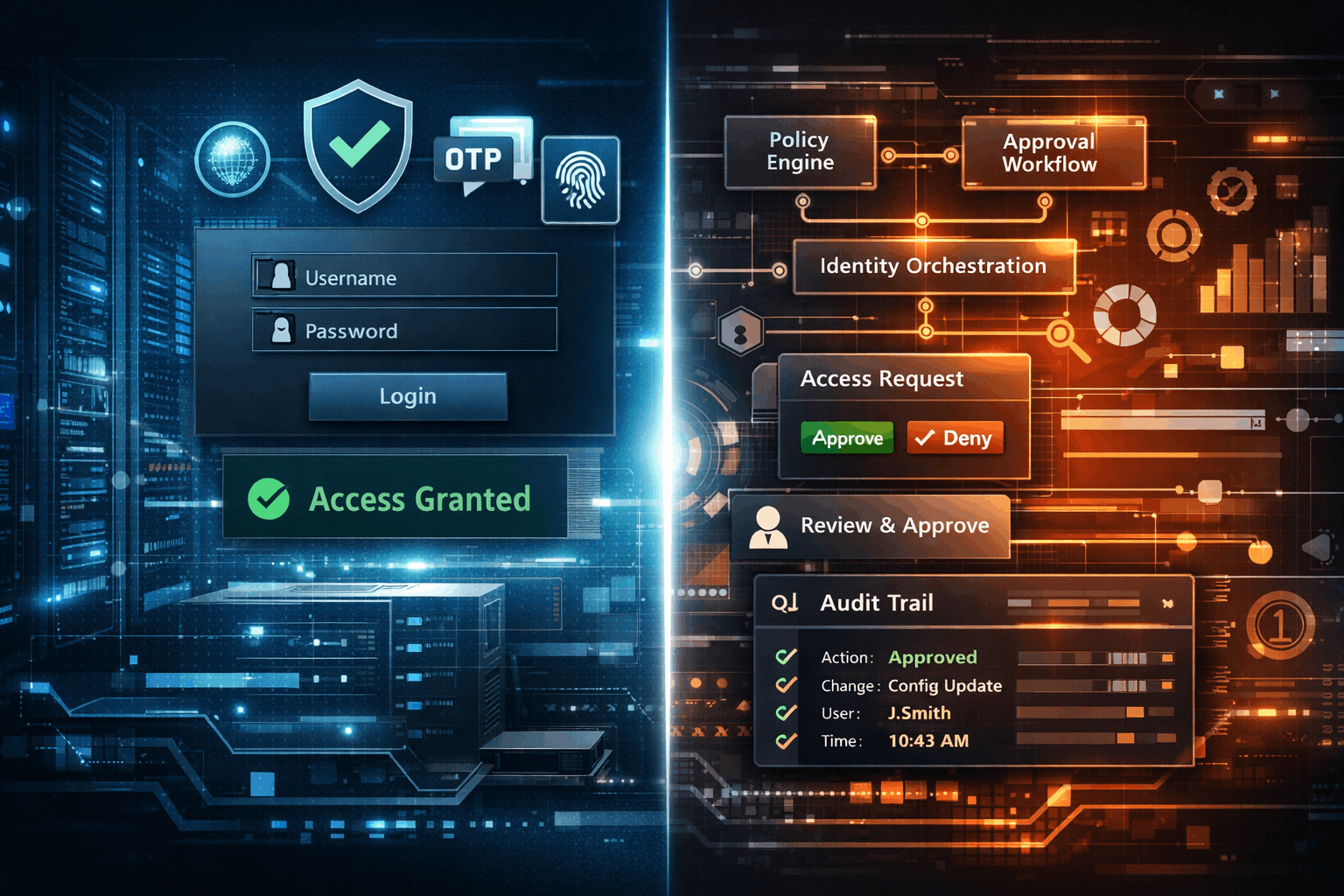
Authentication operates at the point of entry.
Once the system authenticates a user.:
- They establish sessions.
- Someone issues tokens.
- People often implicitly trust access.
From there, downstream systems make fragmented authorization decisions — often inconsistently.
This creates structural risks:
- Over-permissioned identities
- Uncontrolled action execution
- Lack of contextual enforcement
- No unified audit trail
Authentication opens the door.
It does not govern what happens inside.
Identity Execution: The Missing Layer
Modern enterprises operate across:
- Internal systems
- Third-party platforms
- APIs and integrations
- Automated workflows
In this environment, identity is constantly executing actions, not just accessing systems.
Examples:
- Placing orders
- Approving transactions
- Triggering workflows
- Modifying configurations
Each of these actions requires:
- Context
- Policy enforcement
- Approval logic
- Traceability
This is where identity execution governance becomes essential.
Governance-First Identity: A Shift in Control
CCA introduces a fundamentally different approach:
Identity is not just authenticated — it is governed at the point of execution.
This means:
- Every action is evaluated against policy
- Execution is controlled centrally
- Decisions are auditable and deterministic
Key Characteristics
1. Policy-Driven Execution
Actions are allowed or denied based on:
- Role
- Context
- Timing
- Organizational rules
2. Real-Time Enforcement
Decisions happen at execution time, not just at login.
3. Centralized Governance Layer
Control is not fragmented across systems — it is unified.
4. Complete Auditability
Every action is:
- Logged
- Traceable
- Attributable
Authentication vs Governance: A Structural Comparison
| Capability | Authentication Systems | Governance-First Identity (CCA) |
|---|---|---|
| Identity Verification | ✔ | ✔ |
Access Control |
Limited | Contextual & Dynamic |
| Execution Control | ✖ | ✔ |
| Policy Enforcement | Fragmented | Centralized |
| Audit Trail | Partial | Complete |
| Workflow Governance | ✖ | ✔ |
Why This Matters Now
Enterprise environments have changed:
- Systems are decentralized
- Actions are API-driven
- Workflows are automated
- Identities are non-human (services, bots, integrations)
Traditional identity systems were not designed for this level of complexity.
Without governance:
- Actions become untraceable
- Policies become inconsistent
- Risk becomes invisible
CCA’s Role in Identity Execution Governance
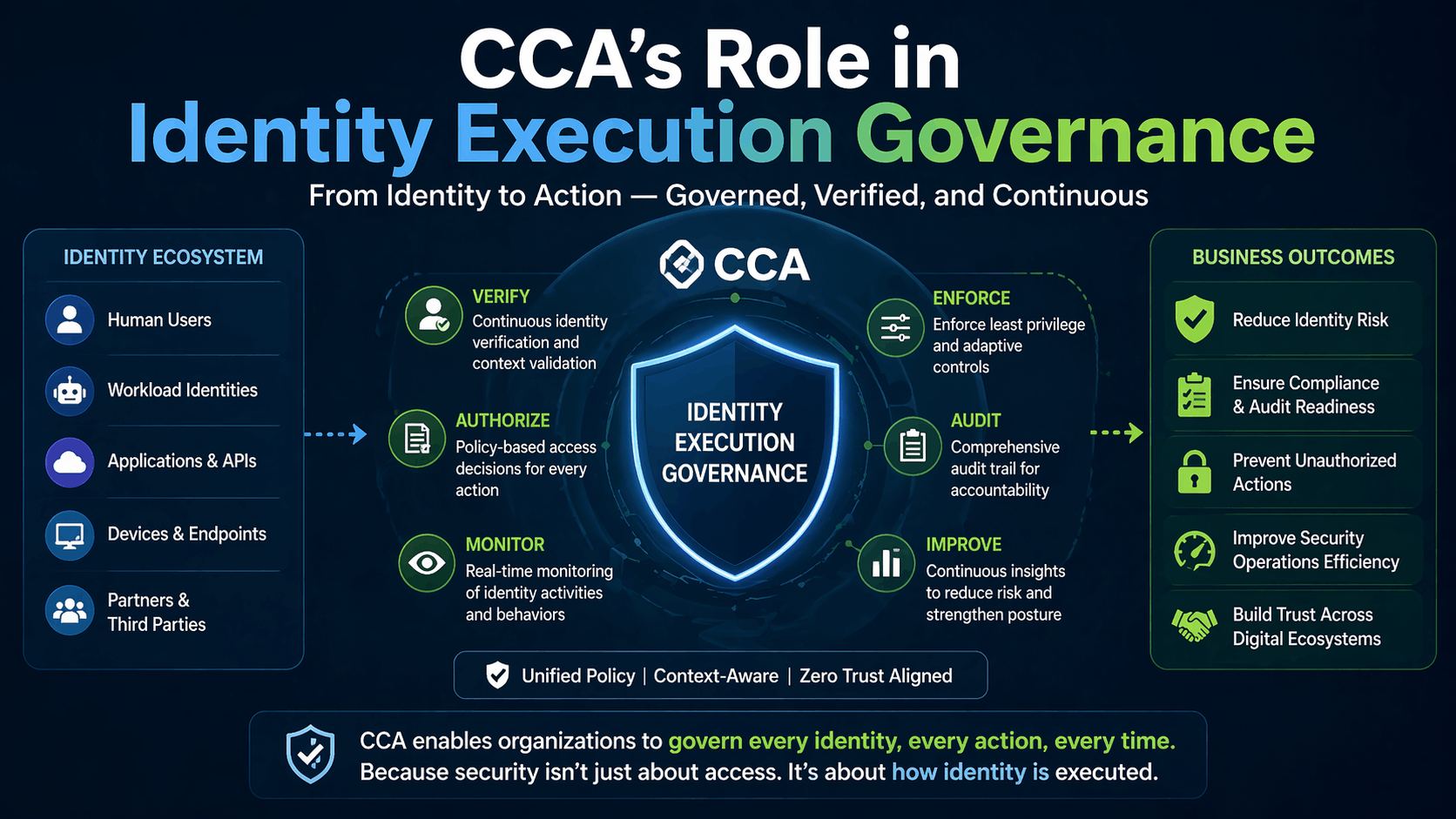
CCA operates as an infrastructure-level control layer that sits between:
Identity → Action → System Execution
It ensures that every action:
- Passes through governance
- Adheres to enterprise policies
- Records are kept and audited.
CCA Enables:
- Unified identity execution control
- Cross-system policy enforcement
- Deterministic action governance
- Enterprise-grade audit readiness
From Access to Accountability
The future of identity is not just about access.
It is about:
- Control
- Accountability
- Governance
Authentication will always remain necessary.
But on its own, it is no longer sufficient.
Conclusion
Enterprises that continue to rely solely on authentication-based identity models will face increasing challenges in:
- Controlling execution
- Enforcing policy
- Maintaining compliance
- Managing risk
The shift is clear:
From verifying identity → to governing identity execution
CCA represents this shift — providing a governance-first foundation for how identity operates across modern enterprise systems.