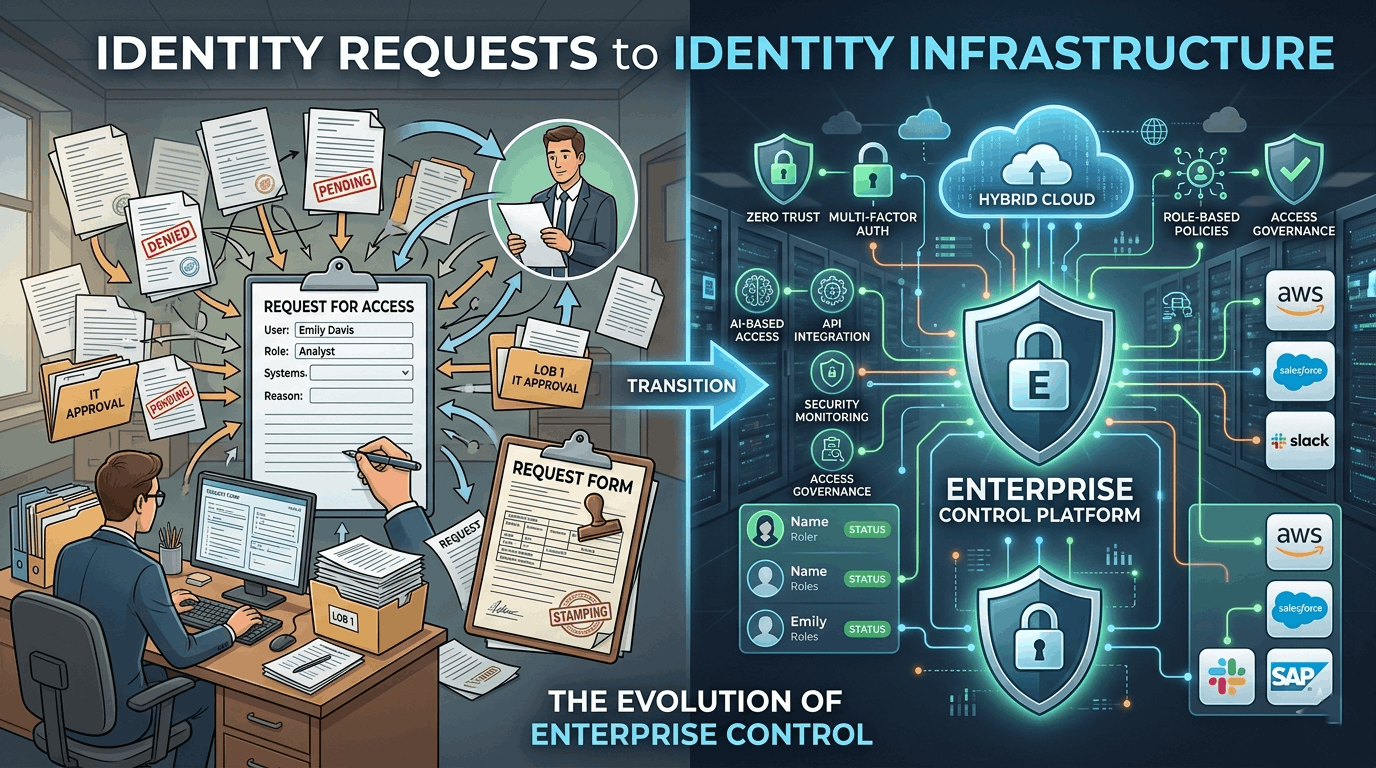
From Identity Requests to Identity Infrastructure: The Evolution of Enterprise Control
Introduction
Enterprise organizations rarely begin with infrastructure. They begin with requests. An employee needs a business card, a new joiner requires onboarding assets, or a department requests branded materials. At an early stage, teams handle these requests manually, often through emails, shared templates, or informal coordination.
This model works temporarily. However, as organizations scale, the volume, complexity, and interdependencies of these requests increase. What was once manageable becomes fragmented. Identity execution begins to drift away from control.
The transition from request-based execution to infrastructure-driven governance is what defines operational maturity in enterprise environments.
The Limitations of Request-Based Identity Execution
Request-based systems rely heavily on human intervention. Each action depends on someone initiating, reviewing, approving, and executing a task. While this provides flexibility, it introduces variability.
In enterprise environments, variability leads to inconsistency. Identity assets such as business cards, email signatures, and access credentials are created through disconnected processes. Different teams follow different standards. Approvals vary. Vendors operate independently.
This results in identity outputs that do not consistently represent the organization. More importantly, it creates a lack of visibility. Organizations cannot easily track what has been created, who approved it, or how it aligns with policy.
Request-based models are reactive. They respond to needs but do not enforce control.
What Defines Identity Infrastructure

Identity infrastructure replaces ad hoc processes with structured systems. Instead of reacting to requests, the organization creates, approves, and distributes identity definitions.
Infrastructure introduces predictability. Every identity-related action follows a defined path. Data originates from authoritative systems. Standardize workflows. Control outputs.
In this model, identity execution is not dependent on individuals. It is governed by systems.
Infrastructure also ensures integration. Identity processes connect with HR systems, procurement platforms, workflow engines, and compliance tools. This alignment allows identity execution to operate as part of a broader enterprise ecosystem.
The Shift from Actions to Systems
The transition from requests to infrastructure is not a single change. It is a shift in how organizations think about execution.
Instead of asking, “How do we fulfill this request?” the organization asks, “How should this process operate at scale?”
This shift leads to the creation of governance layers that sit between requests and execution. These layers enforce rules, manage templates, control access, and route approvals.
Over time, individual actions become part of a repeatable system. What was once manual becomes automated. What was once inconsistent becomes standardized.
This is how enterprises achieve control without sacrificing scalability.
Operational Impact of Infrastructure-Driven Identity
When identity infrastructure is implemented, organizations experience a fundamental change in operations. Processes speed up, not because someone rushes them, but because they are structured. Errors decrease because variability is reduced. Visibility increases because every action is tracked.
Identity assets begin to reflect the organization consistently across all touchpoints. Whether a business card, a digital asset, or an onboarding output, each element aligns with defined standards.
Infrastructure also allows for adaptability. The organization can implement changes to policy, branding, or workflows centrally and apply them across without disruption.
This level of control is not achievable through request-based systems.
Governance as the Foundation of Infrastructure
Governance is what enables infrastructure. Without governance, systems cannot enforce consistency or control.
Governance defines the rules, roles, and workflows that guide identity execution. It ensures that every process aligns with organizational objectives and compliance requirements.
In enterprise environments, governance is not optional. It is foundational. It provides the structure needed to transform fragmented processes into cohesive systems.
By embedding governance into infrastructure, organizations ensure that identity execution remains consistent, compliant, and scalable.
Strategic Takeaway
The evolution from identity requests to identity infrastructure is a defining step in enterprise maturity. Organizations that remain dependent on request-based models struggle with inconsistency, inefficiency, and risk.
Those who invest in infrastructure gain control. They standardize execution, integrate systems, and create visibility across all identity-related activities.
Identity is not just an output. It is a system. Like all enterprise systems, we must govern, integrate, and design it for scale.